Google warns of another zero-day vulnerability in Chrome, only days after addressing a similar issue.
The post Google Patches Second Chrome Zero-Day Vulnerability of 2023 appeared first on SecurityWeek.
Google warns of another zero-day vulnerability in Chrome, only days after addressing a similar issue.
The post Google Patches Second Chrome Zero-Day Vulnerability of 2023 appeared first on SecurityWeek.
NSO Group used at least three iOS zero-click exploits in Pegasus attacks in 2022: FindMyPwn, PwnYourHome, and LatentImage.
The post NSO Group Used at Least 3 iOS Zero-Click Exploits in 2022: Citizen Lab appeared first on SecurityWeek.
A Windows zero-day tracked as CVE-2023-28252 and fixed by Microsoft with its April Patch Tuesday updates has been exploited in Nokoyawa ransomware attacks.
The post Windows Zero-Day Exploited in Nokoyawa Ransomware Attacks appeared first on SecurityWeek.
Google has linked several zero-day vulnerabilities used last year to target Android and iOS devices to commercial spyware vendors.
The post Google Links More iOS, Android Zero-Day Exploits to Spyware Vendors appeared first on SecurityWeek.
Mandiant has conducted an analysis of the zero-day vulnerabilities disclosed in 2022 and over a dozen were linked to cyberespionage groups.
The post Exploitation of 55 Zero-Day Vulnerabilities Came to Light in 2022: Mandiant appeared first on SecurityWeek.
Mandiant links exploitation of the Fortinet zero-day CVE-2022-41328, exploited in government attacks, to a Chinese cyberespionage group.
The post Exploitation of Recent Fortinet Zero-Day Linked to Chinese Cyberspies appeared first on SecurityWeek.
Apple has released updates for macOS, iOS and Safari and they all include a WebKit patch for a zero-day vulnerability tracked as CVE-2023-23529.
The post Apple Patches Actively Exploited WebKit Zero-Day Vulnerability appeared first on SecurityWeek.
Exploitation attempts targeting a critical-severity Oracle E-Business Suite vulnerability have been observed shortly after proof-of-concept (PoC) code was published.
One of the major Oracle product lines, the E-Business Suite is a set of enterprise applications that help organizations automate processes such as supply chain management (SCM), enterprise resource planning (ERP), and customer relationship management (CRM).
Tracked as CVE-2022-21587 (CVSS score of 9.8), the exploited flaw was identified in the Web Applications Desktop Integrator of Oracle’s enterprise product and was addressed as part of Oracle’s October 2022 Critical Patch Update.
According to a NIST advsory, unauthenticated attackers with network access via HTTP can easily exploit the security defect to compromise the Web Applications Desktop Integrator and take it over.
This week, CISA added CVE-2022-21587 to its Known Exploited Vulnerabilities (KEV) catalog, urging Oracle customers to apply the available patches as soon as possible.
The first exploitation attempts, however, were observed on January 21, Shadowserver warned last week.
“Since Jan 21st we are seeing exploitation attempts in our honeypot sensors for Oracle E-Business Suite CVE-2022-21587 (CVSS 9.8 RCE) shortly after a PoC was published,” Shadowserver said.
The PoC came from Vietnam-based cybersecurity firm Viettel Cyber Security, which on January 16 published a detailed analysis of the vulnerability and potential exploitation venues.
According to Shadowserver data, the number of observed exploitation attempts is currently low. However, threat actors are known to target unpatched Oracle products, and the number of attacks may increase shortly.
This week, CISA also warned of observed exploitation of CVE-2023-22952, a high-severity remote code execution flaw in SugarCRM.
Impacting the EmailTemplates, the vulnerability is described as a missing input validation defect that allows an attacker to inject custom PHP code using crafted requests. Patches for this vulnerability were released on January 11, 2023.
In January, shortly after exploitation began, Censys reported seeing hundreds of SugarCRM servers being hacked using CVE-2023-22952.
Related: Exploited Control Web Panel Flaw Added to CISA ‘Must-Patch’ List
Related: CISA Says Two Old JasperReports Vulnerabilities Exploited in Attacks
Related: CISA Warns Veeam Backup & Replication Vulnerabilities Exploited in Attacks
The post Exploitation of Oracle E-Business Suite Vulnerability Starts After PoC Publication appeared first on SecurityWeek.
Users of the GoAnywhere secure managed file transfer (MFT) software have been warned about a zero-day exploit that malicious actors can target directly from the internet.
The GoAnywhere MFT is made by Fortra, known until recently as HelpSystems, and it’s designed to enable organizations to automate and secure the exchange of data with their trading partners.
Cybersecurity blogger Brian Krebs broke the news about the zero-day vulnerability on Thursday, saying that the company had temporarily implemented a service outage in response.
An advisory obtained by Krebs — it can only be accessed by authenticated users — describes it as a zero-day remote code injection exploit and says that “the attack vector of this exploit requires access to the administrative console of the application”.
According to the vendor, the vulnerable admin console should in most cases only be accessible from within a company’s network, through a VPN, or only by trusted IP addresses. However, the company has admitted that some GoAnywhere users may be exposing the console to the public internet.
Fortra noted that the web client interface, which is typically accessible from the internet, is not affected by the exploit.
The advisory doesn’t clearly say that the vulnerability has been exploited in the wild, but active exploitation is likely, considering that it has been described as a zero-day. In addition, the vendor provides instructions on how customers can check if their system has been compromised.
The best indicator of compromise (IoC), according to the advisory, is the presence of suspicious administrator accounts that may have been created by malicious actors.
The advisory does not mention a patch, but it does recommend mitigations that should prevent exploitation. There is also no mention of a CVE identifier for the vulnerability in the advisory obtained by Krebs.
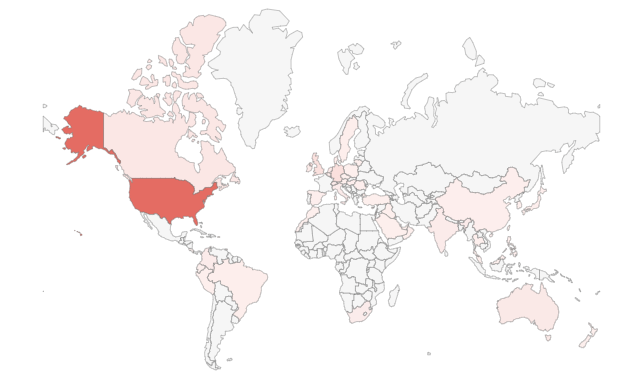
Security researcher Kevin Beaumont has conducted a Shodan search and found roughly 1,000 internet-exposed systems, a majority located in the United States. However, some of the results are clearly labeled as being associated with the web client, which Fotra says is not impacted.
Related: Zero-Day Vulnerability Exploited to Hack Over 1,000 Zimbra Email Servers
Related: US Agencies Warn of APTs Exploiting Recent ADSelfService Plus Zero-Day
Related: Accellion Failed to Notify Customers of FTA Zero-Day
The post GoAnywhere MFT Users Warned of Zero-Day Exploit appeared first on SecurityWeek.